The virus isn’t the only thing that’s been on a rampage this year. Phishing attacks have risen dramatically in the wake of COVID-19 and there is a need to Protect Yourself from Phishing as criminals take advantage of the disruption in our daily work and home life.
Phishing has been a major problem, rising 350% just in three months, between January and March, 2020.
Pandemic related phishing scams have been a constant danger, and many are very convincing, such as those using the logo and signature of organizations like the World Health Organization or the CDC.
Coronavirus-themed phishing scams run the gamut from those promising a “map of outbreaks in your area” to those posing as an email from an employee’s HR department with a link to a new “infectious disease policy.”
It has gotten so bad that the FBI has already issued several warnings this year related specifically to COVID-19 scams.
As of April 21, they had already reviewed over 3,600 complaints related to these scams that included delivery of malware, stolen login credentials, and more.
Email is such as popular delivery method for these types of phishing scams because it gets a potentially dangerous message in front of an unsuspecting person.
They may be going through their normal day, see an email about a COVID update that looks legitimate, and click a link before thinking.
That one click is all it takes to download dangerous malware into your network. Without proper IT security in place, you could end up with a costly security incident.
Tips to Avoid Falling Victim to a Phishing Attack
Phishing used to be much easier to spot. An email would be from a “Prince” of a foreign country, have multiple misspellings or other giveaways that made it stand out. But that type of phishing email is the exception these days.
Today’s phishing attacks are sophisticated, and they use several tactics to get users to believe the email is legitimate, so they’ll take action. These tactics include:
- Spoofing the email address of a legitimate company in the “From” line
- Using the logo and signature of a legitimate company
- Making emails look identical to those sent by companies like Amazon
- Using personalization in the email (i.e. Dear Sam)
- Using links to trusted services like Dropbox or Google Drive
It requires a multi-layered approach to avoid becoming a phishing victim, which includes both user-based and software-based protections.
Train Staff on Phishing Identification
People are the main target when it comes to phishing attacks. Scammers use every trick in the book to try to fool people with their emails.
So employees need cybersecurity training so they’ll be better able to spot and avoid clicking on a phishing email.
Training should be ongoing, and it should include simulated phishing attacks that help users hone their detection skills.
User tips to avoid phishing emails include:
- Hovering over links to reveal the real URL before clicking
- Looking for any small giveaways, like out of place grammar
- Viewing the source code to see if the sending email address matches the “From” address
Use DNS Filtering
Most of today’s phishing emails don’t have any malware in them. Instead of file attachments, which can get caught in antivirus filters, they use links to malicious websites.
As soon as a user click one of these links, then can end up on a website that automatically downloads malware onto their computer.
A DNS filter will block suspicious sites and redirects users to a warning page. This saves them from an infection even if they’ve been tricked into clicking a dangerous link.
Add an Anti-Spam/Anti-Phishing Email Filter
The more phishing emails you can keep out of user inboxes. The less risk your business has of falling prey to a phishing scam.
Email filters designed to quarantine spam. And phishing emails not only improve productivity to Protect Yourself from Phishing by reducing the junk mail users have to sift though. They can significantly decrease the chance of a phishing-based data breach.
Use Email Authentication to Prevent Spoofing
One of the tricks that scammers use is to spoof the email address of a legitimate company in an email message. A person may look at a message and see a familiar email domain.
Such as one from a web hosting company they use. And be fooled into believing the email is real. This could cause them to click a link and enter their login details into a fake form.
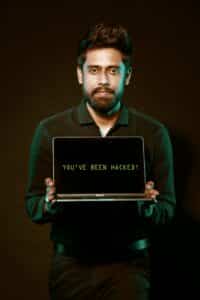
Related: Scary Signs That Your Business Has Been Hacked
Adding email authentication to your email server will stop spoofed email messages from getting through. It uses three protocols – SPF.
DKIM, and DMARC – to identify when the email server sending the message. Doesn’t match the approved email servers for the domain name used in the “From” line of the message. When these don’t match, the message can be rejected or sent to a “junk” folder.
Is Your North Carolina Business Protected from Phishing Attacks?
With phishing running rampant this year, it’s only a matter of time before the next major attack. RCOR has experts that can review your current cybersecurity strategies and let you know if you’re vulnerable.
Contact us today to schedule a consultation. Call 919-263-5570 or contact us online.